Homework: Vulnerability Practice
For this homework, complete the following levels from the Binary Exploitation dojo on pwn.college:
- Your First Overflow (easy) / (hard)
- Precision (easy) / (hard)
- Variable Control (easy) / (hard)
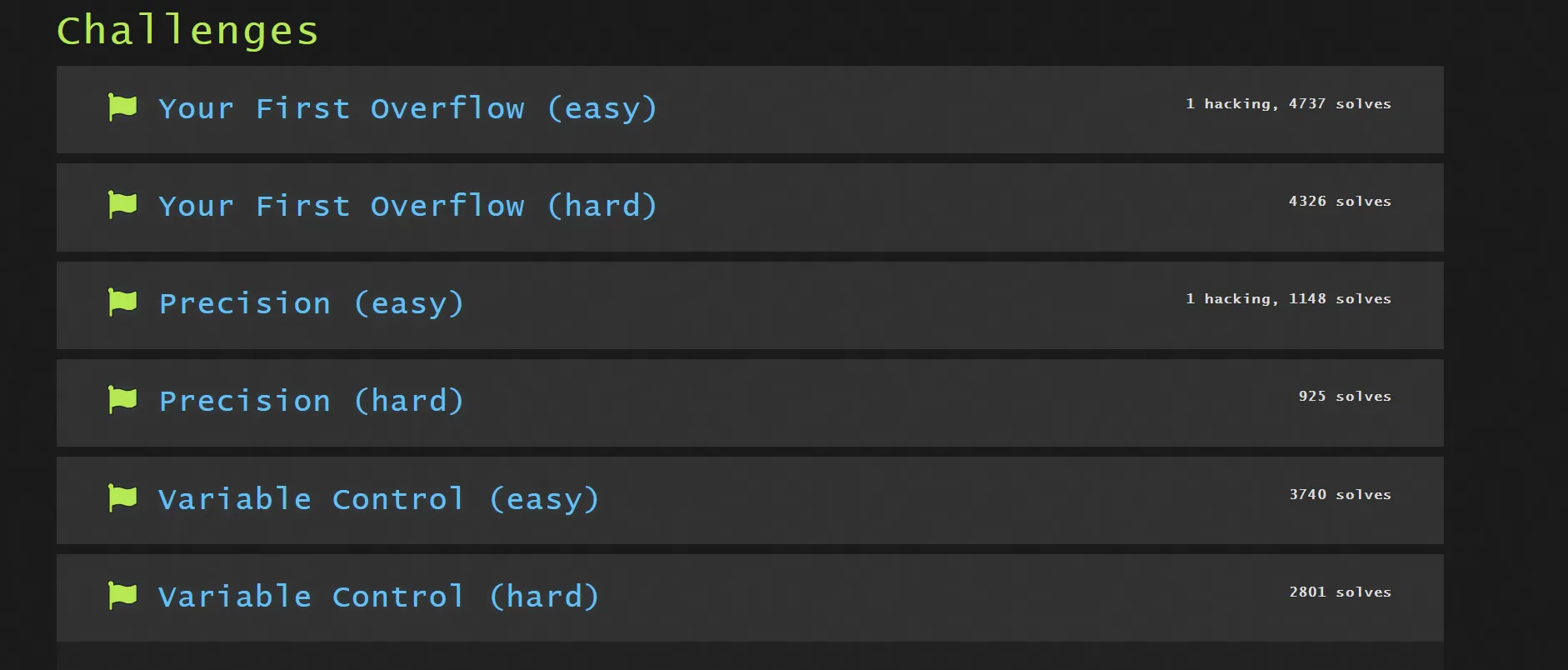
Turn in a screenshot showing your progress: